overleaf template galleryCommunity articles — Recent
Papers, presentations, reports and more, written in LaTeX and published by our community.
A presentation about editing LaTeX documents in Web browsers. Choose how your presentation looks. For more themes, color themes and font themes, see: http://deic.uab.es/~iblanes/beamer_gallery/index_by_theme.html
Mensch Maschine Interaktion

Agreement for Hong Kong Bizarre LLC posted on Crowdfunder.com.
The CPU scheduling is the basis of multi-programming operating systems. By switching the CPU among processes, the operating system can make the computer more productive. The scheduler controls the way processes are managed in the operating system. Linux supports preemptive multitasking, this means that the process scheduler decides which process runs and when. Balance performance across different computer configurations is one challenge in modern operating systems.Linux has two separate process-scheduling algorithms. If a Linux system performs similar tasks in a regular manner, it could be useful to implement optimizations to the Linux scheduler to optimize the performance of those tasks. In this project, we analyze and evaluate the impact of changing the kernel values on the performance of the calculation of 8,765,4321 digits of pi using the Leibniz formula measuring the time that the system takes to perform the calculation.

Midterm research paper for my Adaptive Robotics class at Swarthmore College. Uses the NEAT evolutionary algorithm (http://www.cs.ucf.edu/~kstanley/neat.html) on two robot populations to compete more effectively against each other in a simulated version of capture the flag.
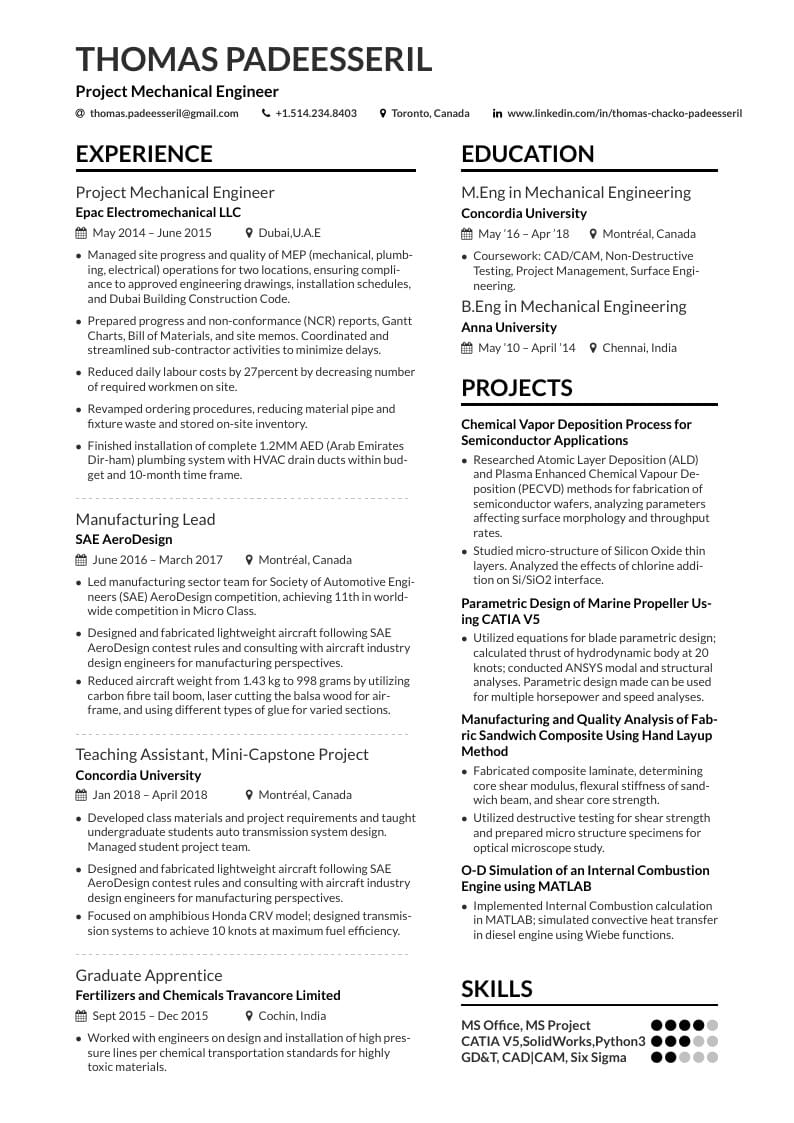
Here is a resume I created from the AltaCV template. I don't know LaTeX so I am pretty happy about my work.
Vorlage für TH Köln Abschlussarbeiten; insbesondere für StudentInnen der Medieninformatik
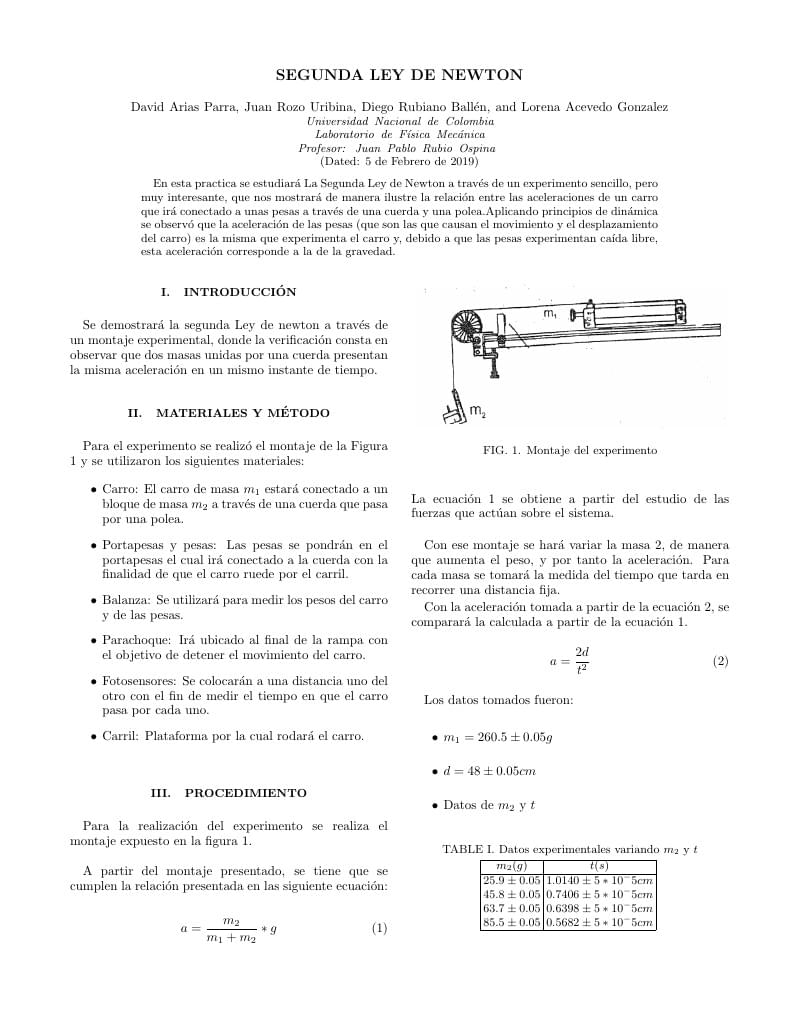
informe de practica pendulo fisico
Computer algorithms that are written with the intent to keep data private are used in every day cryptography. These algorithms may exhibit execution time behaviour which is dependant on secret information that is not known to an outsider. When carefully analysed, this dependency may leak information that can be used to gain unintended access to private data, effectively nullifying the use of such algorithms. This threat poses a vital risk to the field of computer cryptography, and analysis should be done in attempt to eradicate this potential threat from any algorithms in modern day use. In this paper, attacks are orchestrated against several algorithms that have previously been used in cryptography, resulting in the successful retrieval of secret data within a manageable time-scale.
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.